First pass at making a SAM template to detect JAR files which could possibly be affected.. This only checks for existence. There's probably more work to be done, but this is a start.
Uses PowerShell and robocopy, so it's only been tested on Windows systems using the agent. It may work via WSMAN, but I don't have anything in my lab at the moment that can check for that.
I elected to use robocopy because it's significantly faster than Get-ChildItem, but presents a few of its own quirks. It's still not a "fast" script because of the work it needs to do, but I can't find a way to make it faster (at the moment) It's still not recommended to run frequently (default is once per 12 hours) and has a long timeout defined (30 minutes).
If you make any improvements, please feel free to re-upload an additional SAM template and I'll flag this as "Legacy."
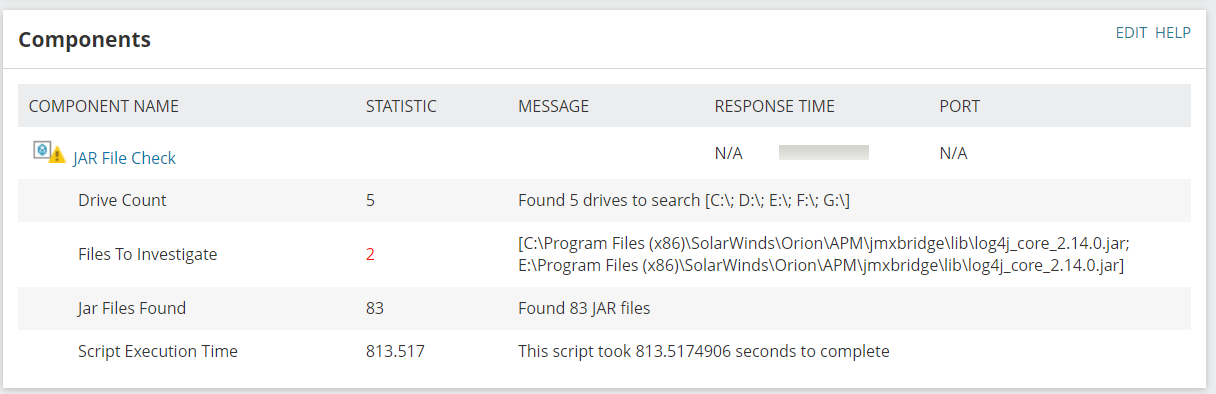
Returns 4 results:
- Drive Count
- JAR Files Count
- Files to Investigate Count
- Script Execution Time
Note: This does not detect nor repair the CVE. It only detects files which may be an indicator that you have an issue.
Final warning: This is still read-only intensive on all of your local drives. You may see performance degradation, which is why it runs so infrequently.