As a part of an effort to help untangle compliance initiatives, a popular request on the federal side is FISMA (Federal Information Systems Management Act) Compliance and support for the Risk Management Framework (RMF). In this post, I’ll outline what FISMA compliance is, we’ll walk through FISMA bit-by-bit, and we’ll talk about where SolarWinds products can help.
products can help.
FIS-WHAT? What Is FISMA and RMF? And How Does NIST Play Into it? And FIPS?
What it means to take on “FISMA Compliance,” is described in several NIST (National Institute of Standards and Technology) publications. The amount of NIST publications out there are impressive, but there are only a few we’re interested in. A couple of these are FIPS (Federal Information Processing Standard) publications—usually when we think of FIPS we think of encryption, but here we’re mostly focused on risk analysis.
- NIST 800-37: Establishes the Risk Management Framework as the security life cycle approach.
- NIST 800-53: This is the main “FISMA Compliance” publication. This describes what controls need to be applied to different systems.
- FIPS 199 and
- FIPS 200: These two documents describe how to perform risk analysis and categorization for systems on the network. You’ll need this categorization when you go to implement 800-53.
Here’s a great summary, though wordy, of how it all fits together:
FIPS Publication 200, Minimum Security Requirements for Federal Information and Information Systems, is a mandatory federal standard developed by NIST in response to FISMA. To comply with the federal standard, organizations follow the Risk Management Framework to determine the security category of their information system in accordance with FIPS Publication 199, Standards for Security Categorization of Federal Information and Information Systems, derive the information system impact level from the security category in accordance with FIPS 200, and then apply the appropriately tailored set of baseline security controls in NIST Special Publication 800-53, Security and Privacy Controls for Federal Information Systems and Organizations |
Okay, okay, how about the super simple version? In order to implement FIPS 200 with NIST 800-53, you have to first do the risk categorization in FIPS 199. Whew!
Navigating and Implementing NIST 800-53 – High Level
We’ll leave the whole exercise of assigning risk up to you, since it’ll be different for each environment. Once you’ve done that, as you walk through the 800-53 requirements, you’ll see different controls needing to be applied at different levels. Generally, you’ll have to comply with the “document” and “policy” controls across all risk levels, but some of the finer controls may not need to be applied to all risk levels.
NIST 800-53 and the RMF (revision 2) provide a great breakdown of the steps needing to be applied. Of interest to us when it comes to where SolarWinds products can help are:
- Step 4: Implement controls
- Several products, including Network Configuration Manager (NCM), Access Rights Manager (ARM), and Patch Manager, can be used to satisfy controls OR help implement and manage implementation of controls
- Step 5: Assess controls are working correctly
- Our security product portfolio, including Security Event Manager (SEM), Access Rights Manager (ARM), and Network Configuration Manager (NCM) can be used to make sure controls have been implemented correctly.
- Step 7: Monitor
- Lastly, several products, including SEM, ARM, Network Performance Monitor (NPM), and NCM, can be used to make sure controls are working as expected, bypasses aren’t attempted, and produce reports to prove it.
I’ll walk through each control and identify relevant products for each category as I go, so you don’t have to memorize them all just yet.
Key Out of the Box Content for SEM, ARM, and NCM
Before we dig into implementing key controls (Step 3), as a part of assessing and monitoring controls (Step 4 and Step 6), here is out-of-the-box content designed to help in SEM, ARM and NCM:
For SEM:
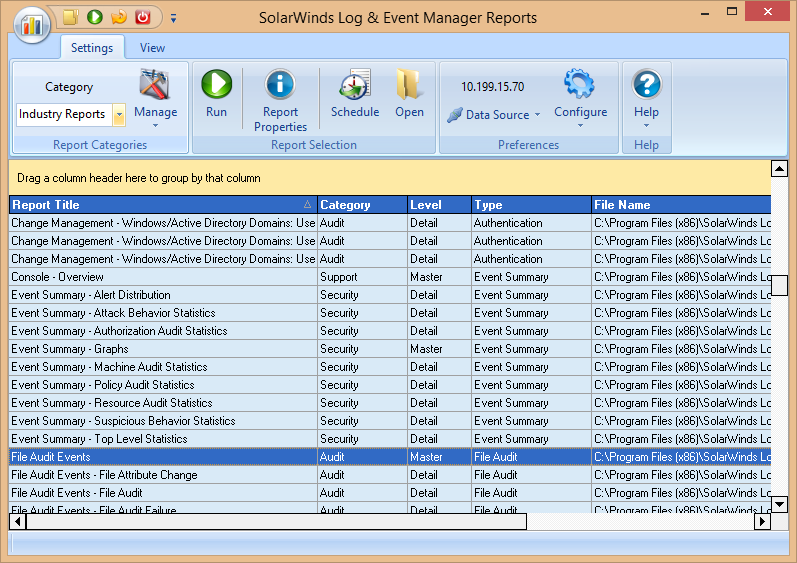
There are hundreds of out-of-the-box reports, many of which are categorized for FISMA specifically. These reports help address the Assess/Monitor by looking for exceptions to controls, unexpected changes or activity, or attempts to bypass controls. In the SEM Reports Console, navigate to Configure > Manage Categories, select FISMA, then click OK. To see the list, go to View > Industry Reports.
In addition, SEM includes dozens of correlation rules categorized for different compliance initiatives. From the SEM Console, navigate to Rules, and Create Rule from Template. I’d recommend starting with General Best Practice, but as we go through the actual controls you should find relevant correlation rules where real-time notifications are useful.
For ARM:
All changes made with ARM are automatically recorded in the log book. This ensures compliance with legal and best-practice standards and saves the time of manual documentation. The log book report allows you to capture events by person or event type within any desired time period. This ensures fully transparent processes and documentation.
In addition, ARM allows reporting by resource or user for all resources.
For NCM:
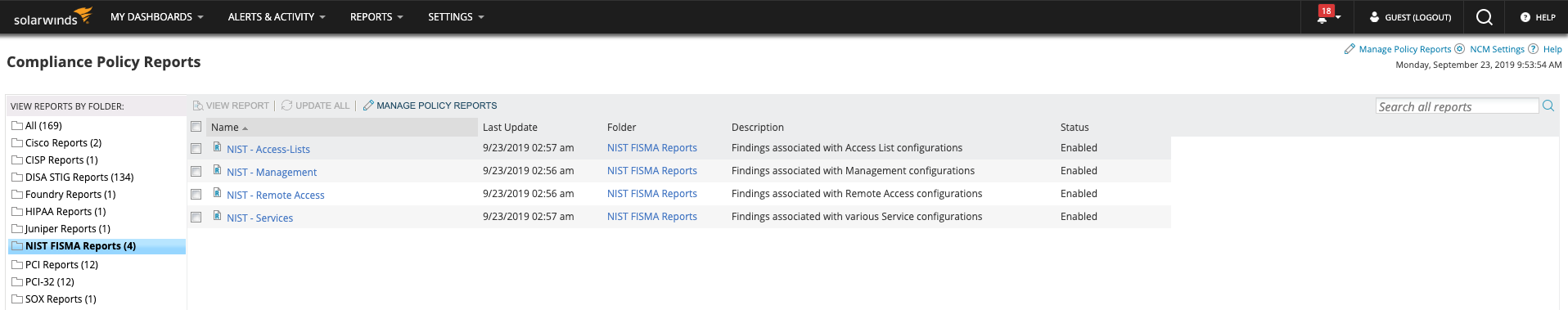
There are several templates included to help (starting with NCM 7.4— DISA STIG and NIST FISMA Reports Now Shipping with NCM!—earlier versions can download from the Content Exchange):
- NIST – Services: identify services exposed on network devices
- NIST – Remote Access: identify remote access enabled on network devices
- NIST – Management: identify management protocols used on network devices
- NIST – Access Lists: identify key access control lists needing to be present
In the NCM web console, under CONFIGS, then Compliance, you should see them listed under the NIST category.
Control-by-Control Details
You might want to get a cup of coffee (or tea) while you read through this, as there’s a lot here. The entirety of Appendix F of 800-53 describes the controls and implementing them in detail. I’m going to skip over many of them since they don’t apply to implementing SolarWinds products, but I’ll include a description for each and more details where they’re especially relevant. Got your warm beverage? Let’s get going.
- AC-X: Access Control
- General Notes: In general, there’s a few areas our products can help, but many of these controls will be implemented at the policy or device level. For some of these, NCM can help you distribute configuration or identify violations when it comes to network devices; SEM and ARM can help audit and monitor for potential changes.
- Of interest:
- AC-1: Access Control Policy and Procedures
- With ARM, you can create and use customized templates for: creating users, creating groups, creating contacts and open order procedures. Templates can be customized to meet access control policies internally and externally, then access management can be standardised and simplified.
- AC-2: Account Management:
- You could use SEM to identify accounts created outside of these controls—e.g., service accounts being added to unexpected groups—either in real-time or via reports
- You could use SEM to audit when passwords were changed on accounts, when users were added to groups, etc—either in real-time or via reports
- You could use ARM to identify permission sprawl and accounts with excessive permissions within Active Directory
 , Exchange
, Exchange , SharePoint
, SharePoint , and File Servers
, and File Servers - SEM can help satisfy AU-2(2): Automated Auditing for creation, modification, enabling, disabling, and removal, either in real-time or via reports
- SEM can assist with AU2(12): Atypical Usage by looking for logon activity or patterns outside your environment norms, either in real-time or via reports
- ARM can assist with AC-2(3): Disable inactive accounts by identifying inactive accounts and deleting or disabling those redundant accounts
- AC-4: Information Flow Enforcement
- SEM can help with AC-4(17)—ensure local authentication isn’t used by auditing for local authentication activity on systems (logons not to the domain), either in real-time or via reports
- AC-6: Least Privilege
- SEM can help audit where things deviate from least privilege—e.g., when an unexpected user accesses certain files, systems, or commands, either in real-time or via reports
- ARM can help to identify accounts with excessive privileges and go against the principle of least privilege and manage user access rights across the IT infrastructure
- NCM can help audit device policies for existing privileged users as things change, and roll out configuration changes if necessary
- AC-7: Unsuccessful Logon Attempts
- Usually this is implemented in IAM/Domain/system policy, but you can use SEM to confirm this policy is being enforced and see how frequently it’s used, generally via reports/historical analysis
- AC-8: System Use Notification
- Where required across network devices, NCM can help distribute config or identify configs not matching expected settings
- AC-9: Previous Logon (Access) Notification
- Where required across network devices, NCM can help distribute config or identify configs not matching expected settings
- AC-10: Concurrent Session Control
- Where required across network devices, NCM can help distribute config or identify configs not matching expected settings
- AC-11: Session Lock
- Where required across network devices, NCM can help distribute config or identify configs not matching expected settings
- AC-12: Session Termination
- Where required across network devices, NCM can help distribute config or identify configs not matching expected settings
- AC-16: Security Attributes
- Depending on how controls are implemented, it’s possible SEM can help identify when things deviate from expected policy, either in real-time or via reports
- AC-17: Remote Access
- SEM can help audit/monitor remote access, but not implement controls. SEM can also help audit where remote access is being used outside of expected controls (e.g., controls are being bypassed, or attempts to bypass are being made). As usual, this can be done either in real-time or via reports.
- Explicitly, SEM can help with AC-17(1)—automated monitoring / control
- NCM can help audit where and how remote access is being used across network devices, identify violations, and potentially roll out policy changes if necessary.
- AC-19: Access Control for Mobile Devices
- You may be able to use User Device Tracker (UDT) to detect usage of devices in those classified networks/facilities, and possibly also use SEM to identify authentication from unexpected users or devices
- AC-20: Use of External Information Systems
- SEM can help audit AC-20(2) and AC-20(3)—use of portable storage devices and personal devices with USB-Defender when policy is bypassed/ignored
- AC-23: Data Mining Protection
- You may be able to use SEM with SQL Auditor or Database Performance Analyzer (DPA) to identify when large queries or unexpected activity is being done to a database
- AT-X: Awareness Training
- AU-X: Audit and Accountability
- General Notes: A lot of this set of controls is about what data you might feed into a system like SEM and how the data needs to be preserved. SEM can help satisfy some controls directly. Some of the comments below are about how SEM treats relevant data within the controls, should be implemented to satisfy the controls, or satisfies these requirements specifically.
- A good note from AU-6(10) to keep in mind: remember you can adjust audit levels depending on organizational needs and risks changing. You don’t have to just enable the firehose.
- Of Interest:
- AU-2: Audit Events
- SEM helps serve this, but this control is about what you feed into SEM
- ARM can help you to trace all user access right based events
- AU-3: Content of Audit Records
- Again, SEM stores this data, but generally this is up to logging sources. Where we normalize data, we preserve these fields.
- ARM is logging all access rights changes in a logbook report and additional reports can be set up and customized.
- AU-3(2): Centralized Management of Planned Audit Record Content—about automation. At a low level, you would serve with tools like NCM (for devices), or Group Policy, but SEM can play a factor in automating configuration to ensure the right data is captured from similar systems with connector profiles.
- AU-4: Audit Storage Capacity
- Depending on your storage requirements you would need to ensure SEM has enough storage capacity to meet your needs, and can implement archiving as well
- AU-5: Audit Processing Failures
- SEM can generate events when agents go offline, when there’s an issue storing or processing data, when running out of disk space, and on behalf of other systems when audit logs are cleared, when there are hardware issues we can detect via log data
- AU-6: Audit Review, Analysis, and Reporting
- SEM satisfies this requirement, up to you to decide which systems need to be audited and for what, and ensure the required data is logged for collection
- Correlation with some data sources (e.g., “non-technical sources” in AU-6(9)) may have to be a manual process done as a part of investigation
- AU-7: Audit Reduction and Report Generation
- SEM and ARM satisfy this requirement
- AU-8: Time Stamps
- SEM satisfies this requirement (note—we’ll use timestamps provided by log sources as well, but may only be down to the second)
- AU-9: Protection of Audit Information
- AU-10: Non-repudiation
- For data stored and accessed in SEM, it satisfies this requirement
- AU-11: Audit Record Retention
- Depending on your retention requirements, you’d need to ensure SEM and ARM have enough storage capacity to meet your needs
- AU-12: Audit Generation
- SEM and ARM help satisfy this requirement
- AU-14: Session Audit
- With AU-14(3), you may be able to satisfy some requirements with Dameware

- AU-15: Alternate Audit Capability
- You may want to set up backup logging for devices sending/receiving syslog messages—or architecting SEM—so you can go to point systems, syslog servers, or servers directly to ensure you can still access data
- AU-16: Cross-Organizational Auditing
- Potentially, you can use SEM to foster cross-organizational auditing (exporting, providing limited access, etc)
- CA-X: Security Assessment and Authorization
- General Notes: for the most part, this isn’t an area we can help support, but Continuous Monitoring does fall under this area
- Of Interest:
- CA-7: Continuous Monitoring
- SEM (correlating security data, alerting, reporting) and ARM (user permission monitoring, access based security issues, alerting, reporting) can help facilitate continuous monitoring We also find many federal government customers utilizing Network Performance Monitor (NPM), Server & Application Monitor (SAM), and other parts of our monitoring suite to support enterprise-wide continuous monitoring
- CM-X: Configuration Management
- General Notes: A few products can help here, but primarily NCM when it comes to network devices. Patch Manager and SEM can also pitch in in a few key areas.
- Of Interest:
- CM-2: Baseline configuration
- For devices, NCM can help establish and automate comparing configs to a baseline, and retaining configs
- CM-3: Configuration Change Control
- For devices, NCM can help test/validate/document and automate changes
- CM-5: Access Restrictions for Change
- You may be able to use SEM to audit when changes are made depending on components and policies changed. NCM for devices and things like dual authorization.
- CM-6: Configuration Settings
- CM-6(1): automated central management—use NCM for network devices.
- CM-6(2): NCM can help for devices, and SEM can potentially alert on relevant events in real time.
- CM-7: Least Functionality
- SEM can help audit when unauthorized software and programs are being executed
- CM-8: Information System Component Inventory
- Patch Manager can help audit software and system status
- CM-10: Software Usage Restrictions
- You can use SEM to audit when P2P and other software is used in general, and Patch Manager to audit what’s installed on a system, but it may not ultimately be perfect
- CM-11: User Installed Software
- You can use SEM to audit when much software is being installed, and Patch Manager to know what’s on a system
- CP-X: Contingency Planning
- IA-X: Identification and Authentication
- IR-X: Incident Response
- General Notes: For the most part, SEM can help when it comes to incident generation and investigation, and also leveraging active response can provide you with in-the-moment capabilities to deal with incidents as they occur
- Of Interest:
- IR-4: Incident Handling
- SEM can support this—including IR-4(4) information correlation, IR-4(5) automatic disabling of information system, and IR-4(9) dynamic response capability
- IR-5: Incident Monitoring
- SEM may generate incidents from correlated activity, and this information can be tracked and stored (reports produced, alerts sent, etc)
- IR-6: Incident Reporting
- SEM can help support IR-6(1)—automated reporting to report correlated incidents detected from within SEM. (Where other SW products are used to detect and generate incidents, this is also generally true of them).
- MA-X: System Maintenance
- General Notes: NCM is a key player here to help with controlling and managing approvals where it comes to network devices. SEM can help alert when stuff doesn’t seem according to expected maintenance policies.
- Of Interest:
- MA-2: Controlled Maintenance
- NCM can help with MA-2(2) automated maintenance for network devices, and SEM can help audit when maintenance is taking place outside of expected maintenance windows
- MA-4: Nonlocal Maintenance
- SEM can help audit MA-4(1)—auditing and review of nonlocal maintenance
- NCM can help with MA-4(5)—network device approvals and notifications
- MP-X: Media Protection
- General Notes: Most of this isn’t relevant when it comes to SolarWinds products, but there’s one area when it comes to removable devices where SEM’s USB-Defender can help
- Of Interest:
- MP-2: Media Access
- SEM’s USB-Defender can help with the USB removable media component of this.
- PE-X: Physical and Environmental Protection
- PL-X: Security Planning
- General Notes: Several of the mentioned controls are those which may be supported by LEM, which can be used to centrally manage auditing and monitoring, especially within PL-9. Also interesting when it comes to PL-8 is mention of defence-in-depth techniques.
- PS-X: Personnel Security
- General Notes: A lot of this is external and policy-related, but think about using SEM to ensure what should happen did (i.e., Trust, But Verify).
- Of Interest:
- PS-4: Personnel Termination
- May use SEM to audit usage of credentials and ensure attempts to use them don’t continue after users are terminated
- PS-7: Third-Party Personnel Security
- May use SEM to audit usage of third-party credentials and ensure attempts to use them don’t continue after users are terminated
- RA-X: Risk Assessment
- General Notes: There’s a lot of policy and procedure here, and only one area where SEM and Patch Manager especially can help
- Of Interest:
- RA-5: Vulnerability Scanning
- Can use Patch Manager to assess vulnerable systems by missing patches
- RA-5(1) Update Tool Capability and RA-5(2) Update by Frequency/Prior to New Scan/When Identified—Patch Manager is automatically updated with new patches
- RA-5(6): automated trend analysis—Patch Manager can report on patch status over time
- RA-5(8): review historic audit logs—Patch Manager will include audit activity of what is being patched and tracked
- Also, you can use SEM with a vulnerability scanner to support RA-5(6) and RA-5(8) as well, along with RA-5(10) correlate scanning information
- SA-X: System and Services Acquisition
- General Notes: Not a lot of this applies to us, but it’s worth mentioning SA-4(8) speaks to ensuring new systems/apps include activity monitored as part of continuous monitoring planning. Think about how you’re going to monitor systems as you implement them.
- SC-X: System and Communications Protection
- General Notes: SC is a set of controls with everything from cryptography, to honeypots, to detonation chambers. There’s a few places I made notes where SolarWinds products are relevant
- Of Interest:
- SC-5: Denial of Service Protection
- SC-7: Boundary Protection
- Monitoring communications with SEM, NTA/NPM, and NCM for the configuration side.
- SC-7(8): you can also use SEM to monitor attempts to bypass proxy server
- SC-7(10): you can generally use SEM for monitoring here
- SC-19: Voice Over Internet Protocol
- SC-29: Heterogeneity
- Where you have a heterogenous environment, third-party monitoring and management tools like SW (e.g., Virtualization Manager, SAM, NPM, and SEM) are more important
- SI-X: System and Information Integrity
- General Notes: There’s a big section for SEM in here specific to auditing (aside from the normal steps for compliance), but also a couple of other smaller areas of note
- Of Interest:
- SI-2: Flaw Remediation
- Patching—Patch Manager can help with SI-2(1) central management, SI-2(5) automatic software updates, and SI-2(6) removal of previous versions
- SI-4: Information System Monitoring
- This is all about SEM—also SI-4(2) automated tools for real-time analysis, SI-4(4) inbound and outbound communications traffic, SI-4(5) system-generated alerts, SI-4(7) automated response to suspicious events, SI-4(11) analyzed communications traffic anomalies, SI-4(12) automated alerts, SI-4(13) analyzed traffic/event patterns, SI-4(16) correlate monitoring information, SI-4(17) integrated situational awareness, SI-4(19) individuals posing greater risk, SI-4(20) privileged users, SI-4(22) unauthorized network services, SI-4(23) host-based devices, and SI-4(24) indicators of compromise
- You could also use NPM/NTA where traffic comes into play to potentially detect unexpected traffic patterns or performance issues indicating security issues
- SI-7: Software, firmware, and information integrity
- Can use SEM to detect some unexpected changes, e.g., windows does a system file check initially which can create events, and can also use SEM or Server Configuration Monitor (SCM)’s FIM to detect critical system changes (files, registry keys)
- SEM would also support SI-7(5) automated response, SI-7(7) integration of detection and response, and SI-7(8) auditing capability for significant events
- SI-15: Information Output Filtering
- You would want to integrate these into SEM, and consider something like SEM’s SQL Auditor to detect failures when it comes to databases
Double whew! I bet your hot beverage cup is empty at this point, perhaps I should’ve warned you to use a large one.
Got FISMA?
Hopefully at this point we’ve given you more info on how we can help you get moving with FISMA compliance. If you have any questions, feel free to post them and we’ll update the post as things change or more details are necessary.