I have a request for the following rule to be made:
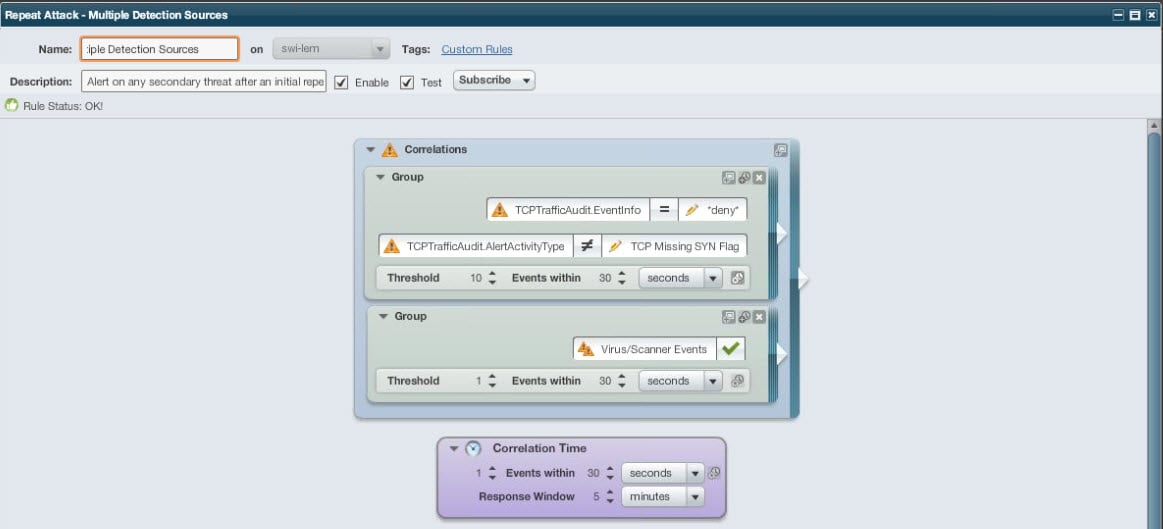
Repeat Attack-Multiple Detection Sources Goal: Find hosts that may be infected or compromised detected by multiple sources (high probability of true threat). Trigger: Alert on ANY second threat type detected from a single IP Address by a second source after seeing a repeat attack. (i.e. Repeat Firewall Drop, followed by Virus Detected) |
Ignoring the obvious issues with how generalized this request is (i.e., what kind of events are determined to be primary and secondary attacks? how many constitutes "repeated"?, etc.), we are trying to at least get a starting point to the setup based on the last line of the request (Firewall drops + Virus detected)
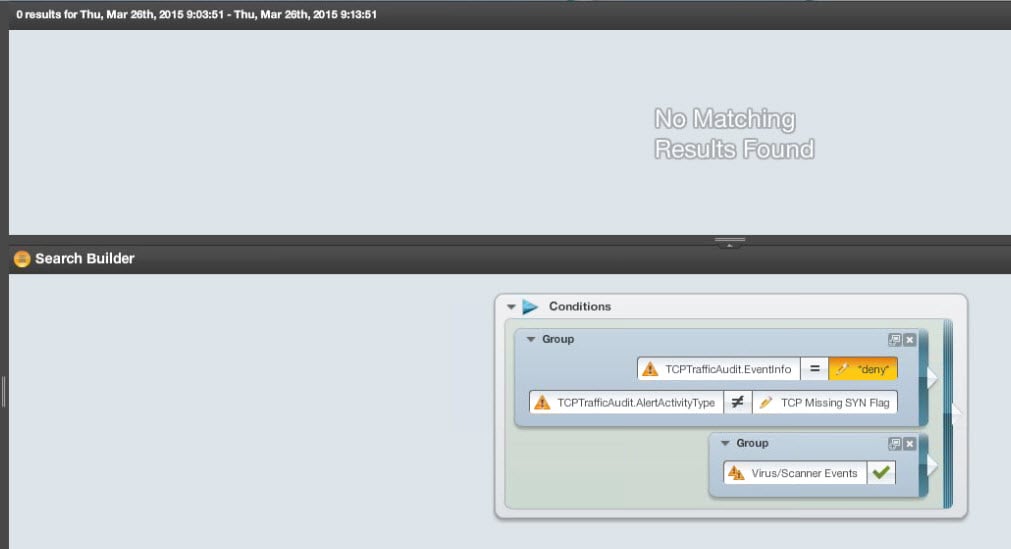
We are currently waiting on a connector to be made for our virus detection. Therefore, there are NO virus events possible in LEM (at this time). However, when I enable the following rule, we got close to 100 emails in about 4 minutes. Can anyone give some insight into the logic (or lack thereof) for the correlation set below?
For reference, here is a similar search in nDepth over the time period we got all of the emails during:
I am assuming that there is something off in either the correlation thresholds, or the correlation time.
Also, for the TCPTrafficAudit events, there is an advanced threshold for the TCPTrafficAudit.SourceMachine field to be the same. (re-infer is disabled)
As always, all help is appreciated!