Forgive me, but I am a noob to Solarwinds and this topic may be repetitive to some, but the other threads pertaining to the topic are not rendering the desired result. Thus, I thought I would start a more current thread as it pertains to an ACL Compliance check. Moreover, my benchmark is very brief usage of CiscoWorks NCM which did not seem to require many steps to construct an ACL compliance check and provide helpful info as to how something was in violation provided the cause.
With Solarwinds, essentially I am trying to establish a compliance check for ACLs that reside on a Cisco ASA. Below are a couple of ACL examples:
access-list vendor-burgers-client extended permit tcp any4 object-group TheFixings_Resources object-group DM_INLINE_TCP_18
OR
access-list vendor-wafflecone-client remark b-ups-maplesyrup.whatever.org
access-list vendor-wafflecone-client extended permit ip any4 host 172.25.106.20
access-list vendor-wafflecone-client remark WHATEVER
access-list vendor-wafflecone-client extended permit tcp any4 host 192.168.5.113 eq https
access-list vendor-wafflecone-client extended permit tcp any4 host 192.168.5.129 eq https
access-list vendor-wafflecone-client extended permit tcp any4 host 192.168.5.134 eq https
access-list vendor-wafflecone-client extended permit tcp any4 host 192.168.10.3 eq www
access-list vendor-wafflecone-client extended permit tcp any4 host 192.168.10.3 eq https
access-list vendor-wafflecone-client extended permit tcp any4 host 192.168.10.4 eq https
access-list vendor-wafflecone-client extended permit tcp any4 host 192.168.10.5 eq https
I've tried entering the ACLs one line at a time, which is cumbersome as the ACLs may be change depending on the circumstances. Some of the ACLs we'd like to have a compliance check are lengthy and there are many different ACLs to be checked.
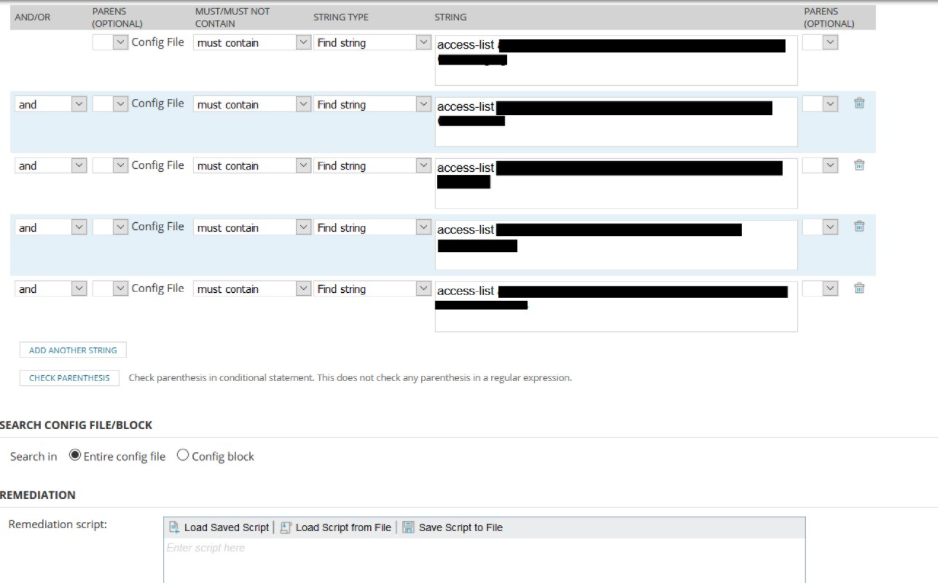
If there is a different entry within any line of the compliance RULE, then the compliance check report will render a "was not found" statement in the compliance check. This is good to know.
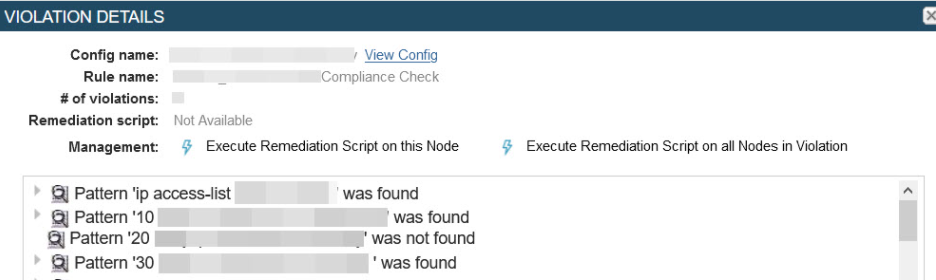
However, Solarwinds did not indicate a violation if there was an extra line on the ASA itself for a particular ACL, thus one less line to check within the compliance RULE. I hoped there would be an indication of a violation. As it stands now to me, if the line count and substance of the lines between ASA and Compliance rule are the same, no violation. If the line count between ASA and Compliance rule are the same, but the there is character difference say udp vs tcp or a different digit (compliance rule may have a 3, but on ASA there is a 4) within a line, then there is a violation and should be reported which does take place.
Additionally, putting the whole ACL in the STRING field has been done, but when there is a violation against the compliance check, it is not immediately known what the exact offense is.
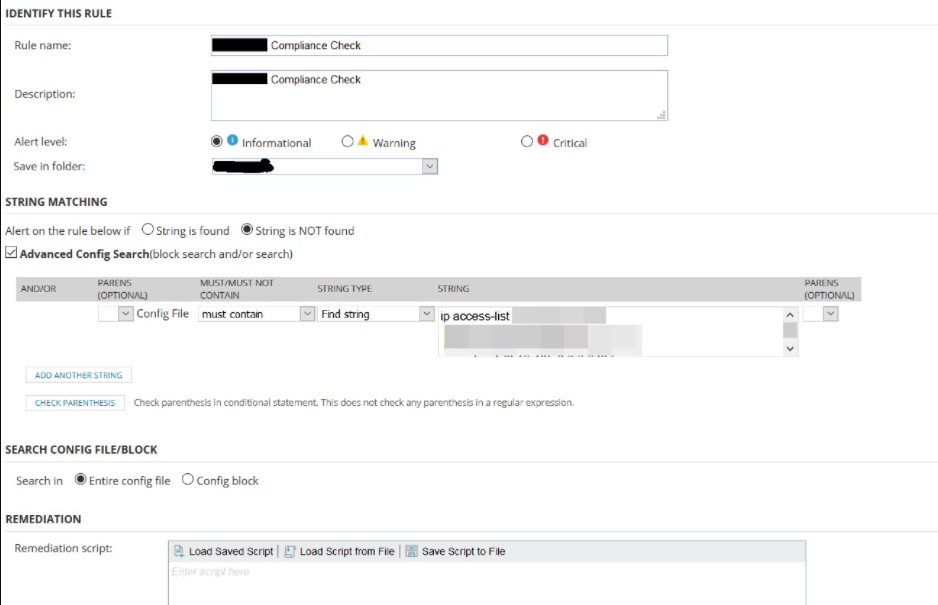
Is there a better, different, more efficient approach for achieving the following across different ACLs that achieve the following?
- ACL order matters
- Check if all the required lines are present and syntax match within the ACL - ASA vs Compliance
- Check if any required line(s) is/are missing - a violation
- Check if any required line(s) are there, but with any extra line(s) - a violation
We then implement a daily compliance email report advising if the compliance has passed or failed. If a failure, what's the cause?
Your time and helpful feedback is appreciated
Thank you.