We have identified that when you create an account with limitations to either specific nodes / interfaces / volumes, the user can simply change the viewid url to see other views.
That is, the user lands on their home page of e.g. ~/Orion/SummaryView.aspx?viewid=99 and they simply change the viewid to something else (viewid=34) and have access to some very sensitive data within the system (see below for detail).
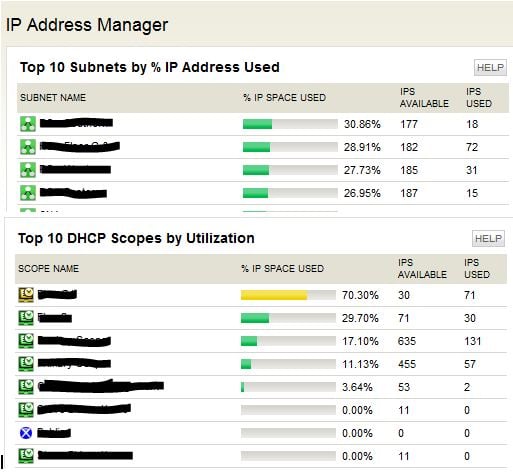
If you have UDT or IPAM installed they can see all your AD accounts, AD Groups, Emails and internal IPs from out-of-the-box views that were installed with these modules.
It seems as though there is no security limitations around particular resources (IPAM, UDT) in the system but it does correctly limit the views nodes / interfaces / volumes.
Here is quick list of resources that a limited user can see by changing the viewid (if you go to Settings > Manage Views in your Orion Web you can see these views and find their viewids - if the modules are installed)
| View Name | Resource on View | Access A Limited Account Has |
|---|
| Virtualization Summary | VMWare Asset Summary | User can see virtual centre details including counts of vcentres, hosts, guests, CPU, memory |
| IP Address Manager | Top 10 Subnets by % IP Address Used | User can see subnets in IPAM and click on them to be taken to “Manage Subnets & IP Addresses” and view all IPs in IPAM |
| IP Address Manager | Top 10 DHCP Scopes by Utilization | User can see DHCP scopes and click on them to be taken to “DHCP Scope Monitoring” and view scopes and IPs |
| Device Tracer Summary | All User Log ins | User can see all users who have logged into devices in our domain (basically all AD accounts). They can click on a user and see AD Groups for that user, their email addresses and devices they have logged into |
| Device Tracker Endpoint Details | All User Log ins | Same resource as above |
We purchased Orion to give customers access to over 450 routers that we manage for them (we all technically work for the same organisation but are separate). We also host some internal websites for this organisation (HR, staffing, information type data through a single portal)
I'm not comfortable giving a customer access to their router and thus technically giving them our AD accounts (from those different views) that they can try and hit our websites with.
I see that I have a few options:
- Feature request to add account limitations that somehow include UDT and IPAM (I've asked support to create this) (this is how I block SEUM transactions as they can also see that)
- Feature request to limit views by users / groups (I've asked support to create this as well)
- Delete the out-of-the-box views from my Orion install (not sure what this will do with upgrades)
- Delete the resources from the out-of-the-box views (this limits the functionality for users like me)
I have found posts from 2009 (http://thwack.solarwinds.com/message/110135) and 2010 (http://thwack.solarwinds.com/message/122936) that detail something similar to my issue and they also created feature requests (now over 2 years old).
Do any other users of this product create limited accounts for internal or external users and have UDT or IPAM installed. Is this a concern for you.....?
Has anyone had this problem and found some workaround to get me out of trouble.
Screenshots: IPAM access for a limited user (they can click on a subnet or scope and see all IPs):
Screenshot: UDT 'All User Log Ins' access to a limit user (they can click on a user and see their AD Groups, Email address and and devices they have logged into)

Thanks for your help,
Ben